Restrict Network Device Communication
Photo by Stock Depot from iStock
Table of Contents
Network port isolation is one way you can restrict communication between network devices. You can restrict certain PCs from accessing your server, for instance, or you may even prevent certain devices from accessing the Internet by blocking communication with the switch port connected to your router.
Port isolation may be used to increase the security of your IoT devices by only allowing access to the port connected to your router. Many IoT devices simply need Internet access but not necessarily access to the rest of your home network such as Roku or AppleTV devices.
I have discovered that port isolation may be used in conjunction with VLANs on my TP-Link T2600G-28TS managed switch (affiliate link) . I do not know if all smart/managed switches support port isolation within VLANs. Other manufacturers refer to port isolation as protected ports.
Some switches such as my TP-Link switch support private VLANs (in addition to port isolation) which allow you to create VLANs within other VLANs so you could further segment your network. One of the biggest differences between private VLANs and port isolation is that port isolation only works on the same switch while private VLANs can work across switches. Depending on your requirements, private VLANs may be overkill for your home network. It is also more complicated to set up than basic port isolation.
Port isolation allows you to group all of your IoT devices, for instance, into the same VLAN, apply the same firewall rules, yet also prevent the devices from communicating directly with one another. If one device gets hacked, it cannot hack other devices within the same VLAN since the ports are isolated.
You could create an individual VLAN for each network device that needs isolated to achieve the same result, but it requires a greater amount of configuration since you would have to create many more VLANs depending on your device count. You would have to apply the same basic set of firewall rules to every VLAN that contains an isolated device. This scenario adds a great deal of redundancy and unnecessary configuration. You should use port isolation within VLANs or private VLANs instead.
Configuring Port Isolation
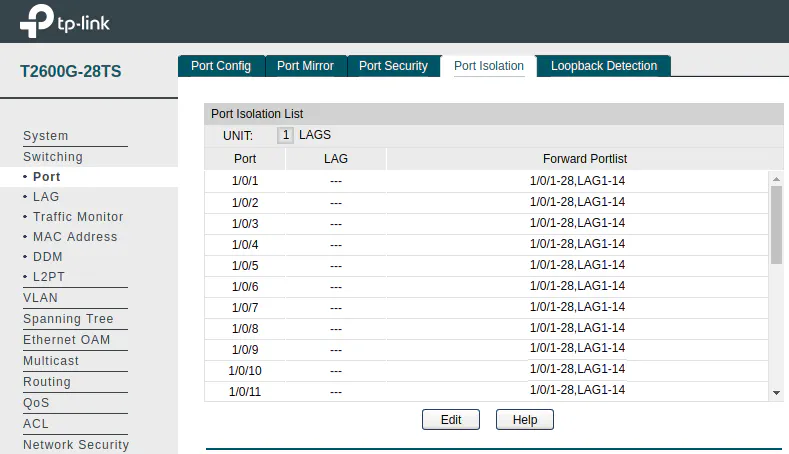
To configure port isolation, go to the “Switching > Port > Port Isolation” page. By default, every port can communicate with every other port.
Click the Edit button to open the port isolation edit page. Notice that you do not pick the port(s) you wish to edit from the main listing page. You will be able to pick the port(s) on the edit page. In the example below, assume port 1 is connected to our router. We are setting port 4 and port 6 to only communicate with port 1. Click the Apply button when you are finished.
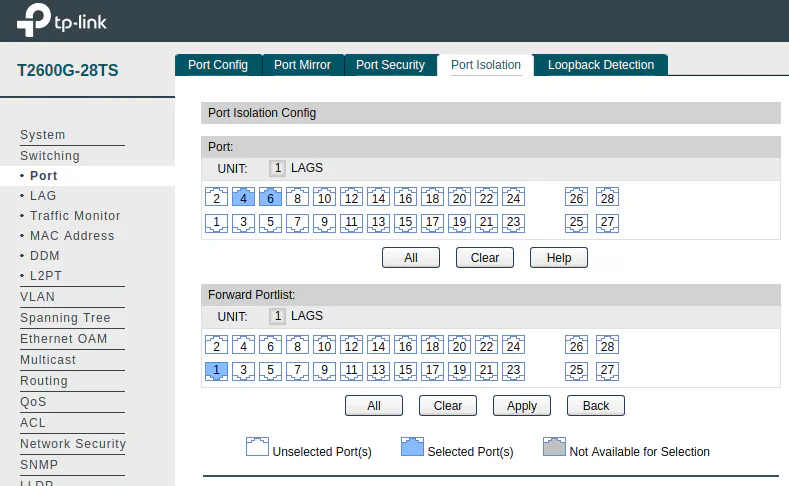
As you can see, you are able to configure more than one port at a time. It is important to note that when you select multiple ports, the same settings apply to all selected ports in the “Port” section. This can be slightly confusing if you are assuming that ports 4 and 6 can also communicate with one another. If port 4 and 6 are in the same VLAN, this configuration would effectively prevent them from communicating directly with each other while still allowing access to the Internet via the port 1 router connection.
Another potential “gotcha” is the fact that you need to configure the communication of the ports in both directions. In other words, you can block port 4 from accessing port 6, but port 6 could still communicate with port 4 if you do not also block port 6 from communicating with port 4. When configuring port isolation, that is something to keep in mind.
As an aside, if you are using VLANs and you are allowing communication between the networks, it is possible for devices that you may have blocked with port isolation to still communicate albeit indirectly depending on your configuration. This could be possible if you allow your devices to communicate with the port connected to your router and you have set firewall rules to allow different VLANs to communicate. Since communication between VLANs is only possible with a router (or a Layer 3 switch), the communication between two isolated devices on different VLANs could occur via the switch port connected to the router. Therefore, be careful when you isolate your devices and configure your firewall rules. You can prevent this scenario from occurring simply by further restricting your firewall rules.


