Enabling All DoS Defend Options on TP-Link Switch without Testing
Table of Contents
In the interest of increasing security and reliability of my home network against malicious attacks, I thought enabling all of the Denial of Service protections on my TP-Link switch would be a good idea. So I enabled the setting and all seemed well enough.
Some time later, my wife tries to use our old 3rd generation Apple TV in our bedroom while folding laundry. It was showing the Computers icon and the Settings icon but not the main Apple TV screen. There was no way of getting past that screen. I have never seen that before so I started poking around the settings and even reset the settings to the factory. I was worried that my DNS filtering software, Pi-hole, was blocking DNS requests used by the Apple TV. Temporarily disabling the DNS filtering (a nice feature built into Pi-hole for troubleshooting) did not help.
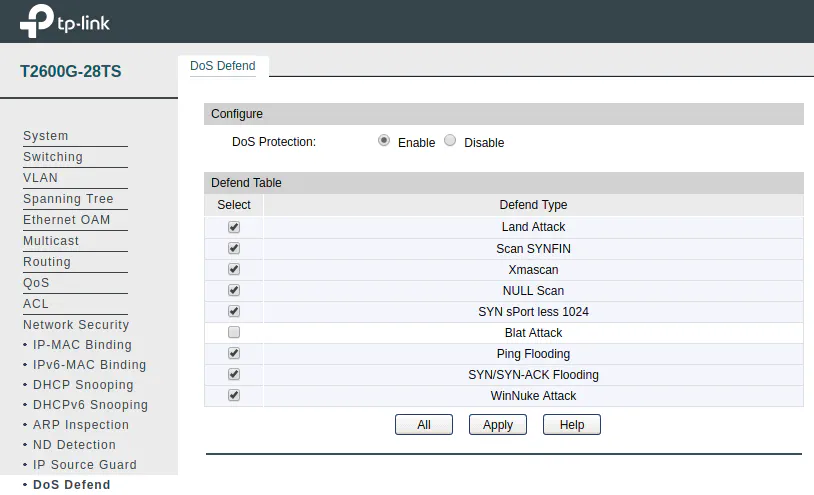
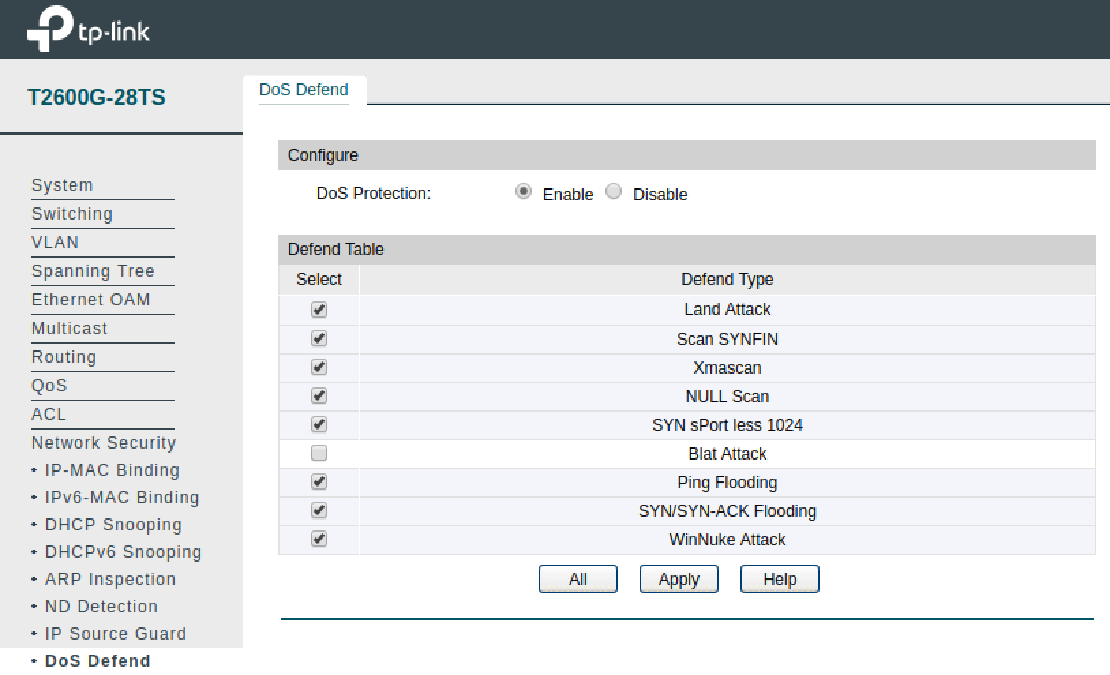
I decided to look at the configuration on my TP-Link T2600G-28TS managed switch (affiliate link) to make sure I was not blocking communication to the appropriate ports since I have several VLANs along with port isolation configured. Since it’s easy to mess up that configuration, I took a closer look. Everything appeared to be fine. Then I recalled enabling all of the DoS Defend options on the switch to further add security protections on my network. Once I turned off all the options, the Apple TV worked fine and was able to communicate with Apple’s servers!
At that time, I did not have time to investigate which setting was the culprit since there are 10 different options you may enable. After doing a quick Google search, I discovered that the culprit may be with the Blat Attack option. The forum post I found discussing this topic mentioned that the Blat Attack option is likely not implemented properly and therefore blocks legitimate network traffic such as Bonjour used by the Apple TV. The author of the forum post states that the Land Attack option most likely covers the Blat Attack scenario anyway.