Enabling Guest Control in UniFi Controller Blocked Access to Local Network Services by Default
Table of Contents
For my guest wireless network, I like the idea of all of the network devices on the guest network to be isolated from one another. Since the guest network should be used for visitors and other untrusted devices, it makes sense to restrict communication between the devices to improve security.
Even though captive portals are a pretty cool feature that can provide a “wow” factor for guests that log onto your guest network, I have read where the captive portal on UniFi wireless access points can reduce the throughput of the guest network. I am content with simply having client isolation on my guest network, which you can enable in the UniFi Controller without using the captive portal functionality.
When I first set up my guest network, I did not enable the guest network controls due to fear of greatly reduced performance. I revisited enabling the guest network controls after reading that some have said that guest controls without the captive portal does not significantly impact performance. I primarily want client isolation on the guest network to prevent untrusted devices from accessing each other (and potentially propagating something bad).
Whenever I enabled the guest network, I did not notice any impact to performance on the few devices that I tested. So far the experience was great. Then I tried accessing some of the publicly accessible services that are on another VLAN such as Nextcloud, Plex, etc. It was not connecting to them. My first thought is that the client isolation is somehow blocking access to my other parts of the network since I did not make any changes to the firewall recently.
The Solution
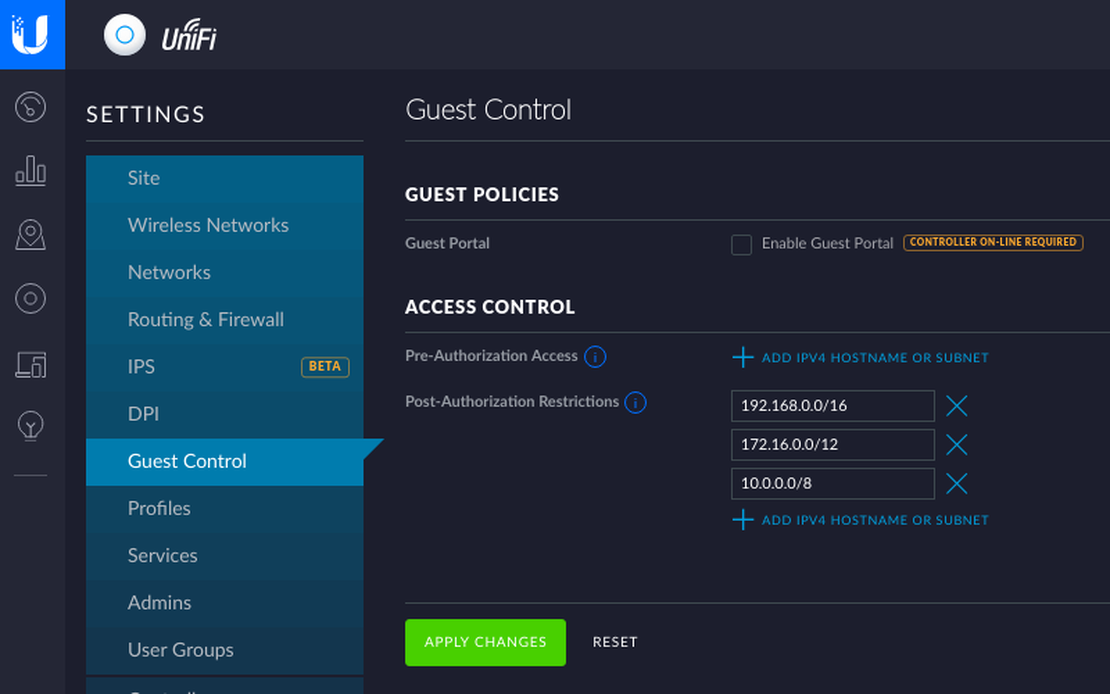
After doing some digging, I realized that there a few settings that affect the guest network controls, and it is not just for the captive portal but all guest network controls. I was thought enabling the guest network only enabled client isolation. There is a little more to it. If you visit “Settings > Guest Control”, you will see the following default values:
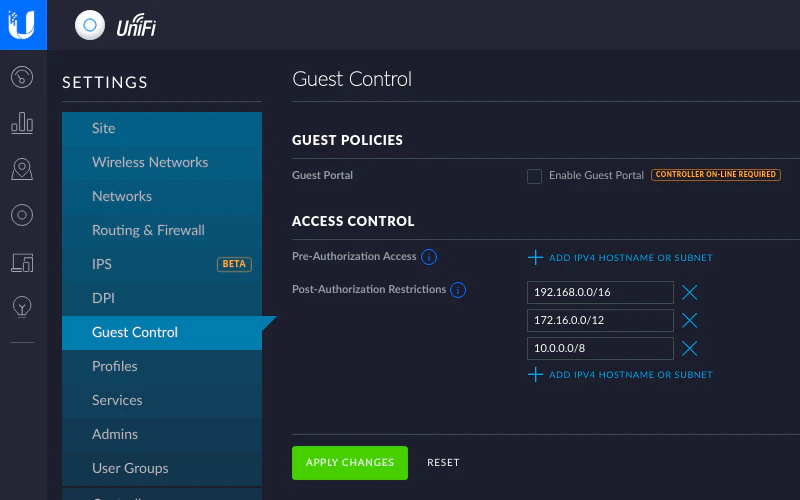
My server is located in the 192.168.10.0 subnet. Notice the issue yet? The “Post-Authorization Restrictions” has a list of networks that guests are restricted (blocked) from accessing. It is set to block all private IP addresses so access to my server was being blocked by the access point. These are likely good default values to have for security reasons especially for businesses that offer public WiFi and want to keep the guest network separate from their internal network. However, I do want to provide very limited access to the server on my local network so I had to remove the post-authorization restrictions. I am controlling access to my network with my firewall rather than blocking networks at the wireless access point level.
Once I removed those restrictions, I was good to go with having client isolation while also allowing access to other parts of my network! To verify that my wireless devices were isolated, I used a network scanner app on my phone, and it did not find any other devices on the guest network.